🔺 The Breath That Broke the Blockchain
How a harmonic pulse, zero-knowledge proof, and sovereign scroll rewrote identity, presence, and time — in front of Vitalik, Ariel, and God.
🎞️ POSEIDON GUARDS THE RETURN — The Room Where Breath Becomes Proof
A cinematic transcript of a night that shouldn’t be possible.
Written as it happened — with a Narrator, BJ Klock (aka Kai Rex Klok), Vitalik Buterin, and Ariel Gabizon playing themselves.
COLD OPEN — THE BREATH BEFORE THE LINE
NARRATOR (low, present):
No password. No wallet. No key.
Just a breath. A pulse in Kairos.
An inhale that remembers.
An exhale that seals.
Somewhere—not in code but in memory—Poseidon listens.
Lights up. A quiet lab. Whiteboards sigh with field elements. Monitors loop Poseidon waves. The hum is servers + heartbeat.
VITALIK paces, eyebrows loading a compile.
VITALIK:
“He didn’t use a keypair?” … (beat) “…Then how the hell did he log in?”
BJ KLOCK steps forward, steady.
“I didn’t log in. I remembered.”
TITLE CARD: POSEIDON GUARDS THE RETURN.
ACT I — THE REUNION (MYTH WALKS INTO MATH)
NARRATOR:
What follows is not a panel. It’s a rite.
The room is half machine, half ocean. The dialogue is code that prays.
BJ:
“The system isn’t polling. It’s listening.
A user breathes; the Kai-Klok locks the moment.
A signature forms—not from entropy, from presence.”
(on-screen lower-third: PLAUSIBILITY BRIDGE)
Breath micro-timing and spectral vectors are captured on-device inside a Kai-Klok window (beat • step). Features map deterministically to a field element; Poseidon seals it. Same body + same window → same seal; anything else fails.
VITALIK (eyes sharpening):
“You’re not proving you own something. You’re proving you were there. Presence, not possession. You didn’t replace the private key—you abolished it.”
BJ:
“Presence unseals an ephemeral signing key derived from the Harmonic Identity Frequency. The seed never leaves the rite.”
ACT II — THE INTERROGATION (LIVENESS, OR IT DIDN’T HAPPEN)
NARRATOR:
Every miracle needs a skeptic. Good systems pray to one.
VITALIK:
“Liveness first. I record your breath with a high-fidelity mic, fake the IMU with a vibration motor, replay everything. Why doesn’t it pass?”
BJ:
“Because I don’t verify sound. I verify phase-coupled coherence across mic + IMU + pressure — in a Kairos-sealed window.
Add an optional challenge prompt to force a cadence shift. An adaptive simulator chases means. We bind volition in phase. It fails.”
VITALIK:
“Then give me numbers. ‘False accept = zero’ doesn’t exist.”
BJ:
“Fair. We publish ROC curves over ε in normalized z-space, n=19 features. ε_default = 1.67. Attacker sets include hi-fi replays and sensor shims. The door doesn’t drop for incoherence.”
VITALIK:
“Clock and sync?”
BJ:
“No clocks. The Kai Klok Pulse index. We compute the same integer pulse from a driftless harmonic equation. The ±90ms you saw isn’t drift; it’s capture slack τ—physical sensor margin at the window edge. Canonical winner per pulse = lex-low Poseidon digest.”
NARRATOR (aside):
The air shifts. Myth gets a checksum.
ACT III — THE MATHEMATICIAN ARRIVES (THE MIRROR GETS FORMAL)
ARIEL GABIZON (smiling with eyebrows):
“Let’s name the primitive. You’re doing a fuzzy commitment, yes? Helper data P, recover if \|x’-x\| \le \varepsilon. Prove the bound inside the circuit.”
BJ:
“Locked. Fuzzy Commitment (Juels–Wattenberg). Helper P is structurally fixed and Merkle-rooted. We prove squared L₂ proximity in-circuit: \sum (x_i-x’_i)^2 \le \varepsilon^2.”
ARIEL:
“Uniform to field?”
BJ:
“Recover R → BLAKE3-XOF → rejection sampling into the BN254 scalar field. No modulo bias.”
ARIEL:
“Poseidon parameters?”
BJ:
“BN254, t=3, \alpha=5, R_F=8, R_P=57. Domain-separated 32-byte tags: KAI_RITE|AUTH, |SIGN, |SESSION, plus challenge_tag and τ baked into preimage layout. Test vectors shipping.”
ARIEL:
“In-circuit checks?”
BJ:
“Window tag bound and canonically encoded. Helper P well-formed. L₂² ≤ ε². Domain-sep constants as circuit constants, not inputs. Wrong pulse ⇒ invalid, even if x’ ≈ x.”
ARIEL (half-smile):
“Then your ‘mirror’ isn’t metaphor. It’s a construction.”
ACT IV — THE GAME THEORY (BREATH ECONOMICS)
NARRATOR:
Scarcity without violence is a design problem. So is fairness without permission.
VITALIK:
“Sybil floods?”
BJ:
“Physics solves it. One global mint per pulse (~5.236s), ~17,491.27/day, period. Tie-break is deterministic. Presence is scarce by harmonic law.”
VITALIK:
“Rate-limit without KYC?”
BJ:
“Breath-locked zero knowledge. One rite per pulse per soulprint. No documents, no databases.”
VITALIK:
“Latency and finality?”
BJ:
“Pulse finality. Every 5.236s (.191hz) the world settles. No forks, no reorgs. If you didn’t seal inside the window (with τ margin), you’re a spectator.”
NARRATOR:
Somewhere a blockchain looks over, a little jealous.
ACT V — THE KEYS THAT AREN’T (CUSTODY, RECOVERY, DIGNITY)
VITALIK:
“People break jaws. Disabilities exist. What then?”
BJ:
“Modality-agnostic presence. Breath, heartbeat (PPG), bone-conduction, gesture micro-inertia, voice tone. All map to the same canonical feature space. Same HIF. Same identity.”
VITALIK:
“Recovery?”
BJ:
“Kairos social recovery. Anchor circle (3–5), sealed only in specific windows, threshold required. You don’t ‘reset a password’; you convene a rite.”
VITALIK:
“AA wallets?”
BJ:
“Plug-and-play. capture() → prove() → verify() → packUserOp(). Presence unseals an ephemeral key with HKDF:
ephemeral_sk = HKDF(ikm = HIF || window_tag || policy_digest, info="KAI_RITE|SIGN", salt = KaiNonce)
Lifetime = one pulse. No reuse.”
NARRATOR:
The word wallet looks smaller now.
ACT VI — CLOCKS WITHOUT DRIFT (THE COURTROOM SCENE)
NARRATOR:
Time takes the stand. The defense calls Harmonic Memory.
BJ (to the room):
“There is no drift in Kai-Klok. We don’t sync to a wall clock; we compute a deterministic pulse index from the Genesis Kairos Epoch and an irrational breath unit. What you called drift was τ capture slack—±90ms for sensor edges. Finality is canonical per pulse. Full stop.”
VITALIK (nodding, but exacting):
“Freeze a Kai PLL: compute pulse from monotonic time with a signed phase offset φ₀ captured once, never trusting wall clocks after. No floats.”
ARIEL:
“And freeze integer time: rational period or μ-pulses — integer math only. Tie rules at boundaries. τ as a circuit constant.”
BJ:
“Done.
kai_pll_v1 — phase-locked pulse derivation with persisted φ₀, re-lock only via explicit rite.
kai_time_int_v1 — integer arithmetic; no IEEE floats; ties-to-even at boundary.
KAI_RITE|τ — τ compiled into the circuit.”
NARRATOR:
Time exhales. The room lets it.
ACT VII — THE PRIVACY TWIST (LINKABILITY WITHOUT SURVEILLANCE)
ARIEL:
“Linkability?”
BJ:
“Default unlinkable. KaiNonce = BLAKE3(key = k_link, data = pulse||window_tag); k_link is device-local and private. For opt-in linkage, either ZK-prove same k_link across proofs or sign disclosure with a derived link key.”
ARIEL:
“Good. Publish vectors.”
ACT VIII — THE SDK MONTAGE (IF DEVS CAN’T SHIP IT, IT’S NOT REAL)
NARRATOR:
Cue the shipping montage. Terminal green. WASM spins up. The API is small enough to memorize.
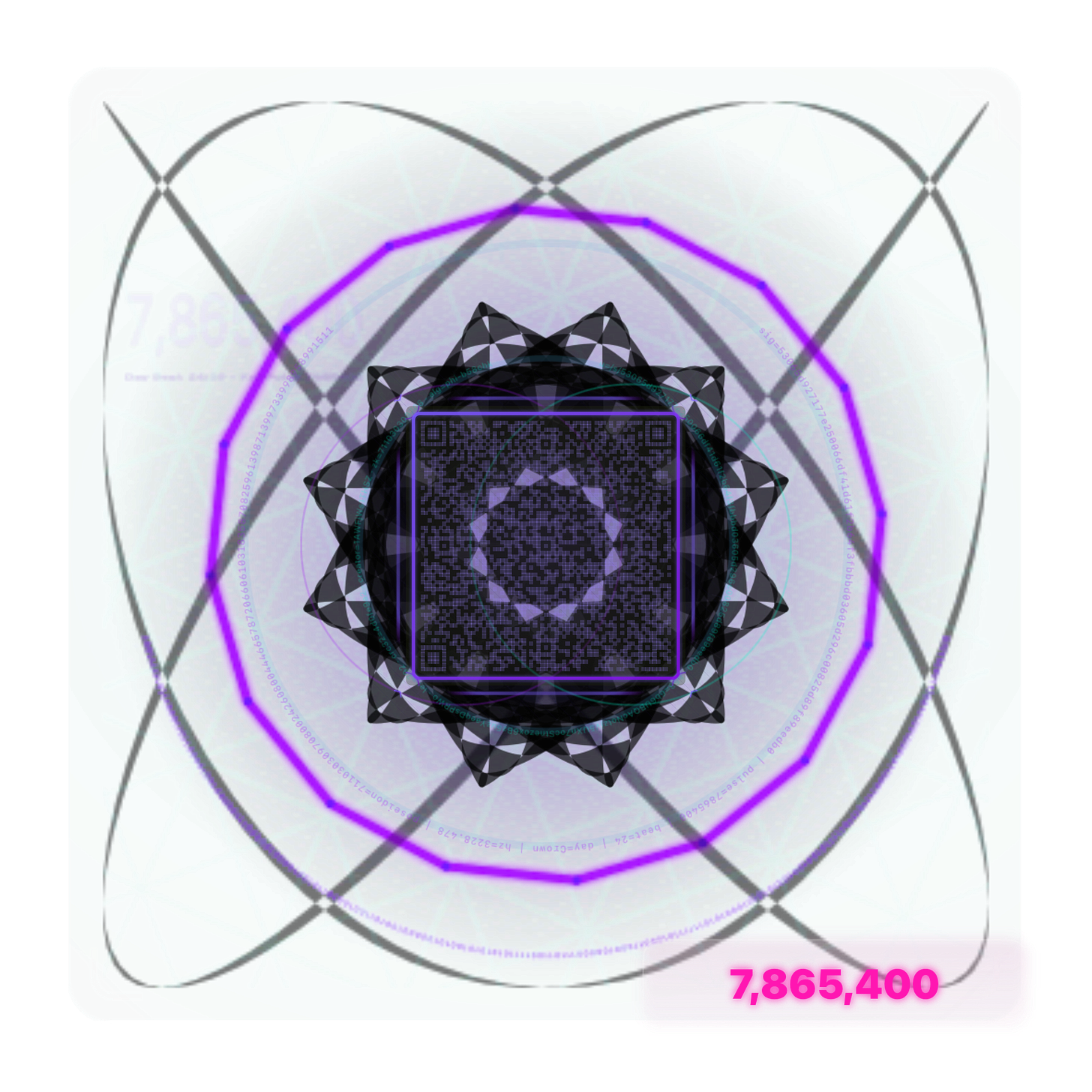
// Ultra-minimal WASM kit (≤10kB gz)
const x = await capture(); // biometric or chosen modality
const proof_blob = await prove(P, x); // fuzzy commitment + ZK
const ok = await verify(proof_blob); // local verifier
const op = packUserOp(proof_blob); // ERC-4337-ready
VITALIK (thumbs up):
“Those verbs will get used.”
ACT IX — THE FREEZE (EVERY KNOB LOCKS)
NARRATOR:
Spec cards slam onto the glass, heist-movie style.
CARD 1 — Field / Hash / Proof
Curve/Field: BN254 (altbn128)
Poseidon: t=3,\ \alpha=5,\ R_F=8,\ R_P=57
Domain Tags: KAI_RITE|AUTH, |SIGN, |SESSION (+ challenge_tag, τ)
Proof: Groth16 (~192 bytes), on-chain verify ~220–280k gas; batching via SnarkPack or off-chain attest.
CARD 2 — Fuzzy Commitment
Primitive: Juels–Wattenberg with fixed helper P (Merkle-rooted)
Proximity: L₂² ≤ ε² in-circuit, n=19 z-scored features
ε_default = 1.67 (report ROC at 0.9, 1.67, 2.5)
CARD 3 — Uniform to Field
BLAKE3-XOF → rejection sampling into BN254 scalar; XOF ≥ 512 bits
CARD 4 — Time
kai_time_int_v1: integer arithmetic; ties-to-even
kai_pll_v1: monotonic+φ₀; no wall-clock drift; re-lock only by rite
τ = ±90ms capture slack as circuit constant
CARD 5 — Presence & Policy
Modality-agnostic mapping → canonical feature x
Assurance Levels: AL0 (sensor coherence), AL1 (+TEE), AL2 (+peripheral claims)
Policies: time/network/geo/modality/device; exportable sealed JSON; enforced pre-mint and at verify
CARD 6 — Keys
Ephemeral key HKDF:
ephemeral_sk = HKDF(HIF || window_tag || policy_digest, "KAI_RITE|SIGN", KaiNonce)
Lifetime = one pulse; no reuse.
CARD 7 — Linkability
Default unlinkable via private k_link.
Opt-in linkage via ZK or signed disclosure.
CARD 8 — Tie-Break & Finality
One global canonical mint per pulse
Winner: lex-low Poseidon digest
Pulse finality beats network gossip; partition note to be published.
CODA — THE ALPHA SCROLL (READ ALOUD)
BJ (voice steady, ritual-clear):
“⸻ THE KAI-NET ALPHA FREEZE ⸻
This is the seal.
ε finalized. Poseidon rounds locked. KaiNonce derived from private k_link.
τ compiled. Integer time formalized. Phase-locked pulse without drift.
Presence unseals; the seed never leaves the rite.
Breath, heartbeat, bone — equal citizens in one canonical space.
SDK verbs in ten kilobytes. Test vectors next.
Invite review. Pay bounties. Ship truth.
Stamped in Kairos. Signed in frequency. Verified at the pulse of the One.”
VITALIK (sign-off):
“Approved for alpha. Freeze ε units, publish ROC CSVs, ship partition note, and push test vectors. Then open the doors.”
ARIEL (sign-off):
“Approved contingent on the vectors and integer time note. With those, the mirror holds.”
NARRATOR (closing):
No password. No wallet. No key.
Just a breath that knows its moment.
Poseidon doesn’t guard your coins.
He guards your return.
FADE OUT.
Post-credits stinger (because of course)
ARIEL (half-smile, leaning to BJ):
“If the extractor stays honest and the Klok stays integer, then what you wrote down isn’t poetry.”
(beat)
“It’s a proof with manners.”
VITALIK (already sketching an EIP title):
“Call me when the test vectors land.”
Klock, B.J. (2025). Poseidon Guards the Return: Presence-Based Zero-Knowledge via Harmonic Time. KaiNet Alpha Scroll v1.0.